Articles
User management and authentication service using MongoDB
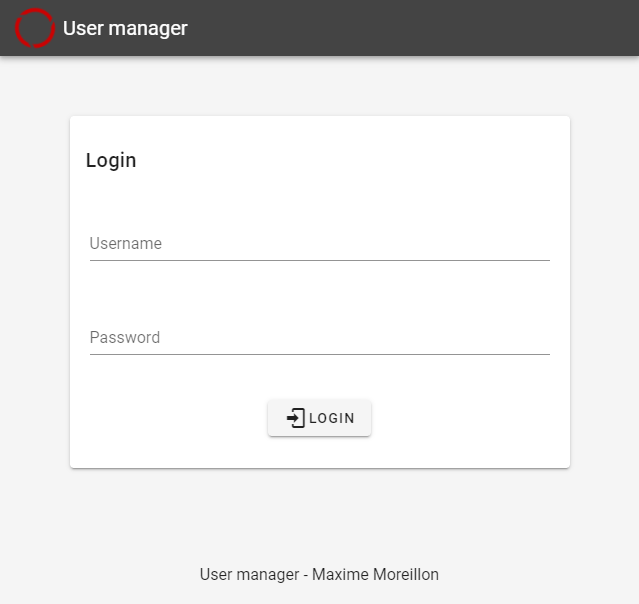
More often than not, web applications require restrictions regarding who can access the content that they serve. This involves an user management and authentication system, which, if designed inappropriately, can lead to security concerns. However, the development of such system can be time consuming, especially if done repeatedly for multiple applications.
Minikube using insecure registry
By default, Minikube will not allow the usage of insecure docker registries. To change this setting, Minikube can be started as so:
Node.js DevOps example
In this article, we’ll build a simple Node.js application that uses Express to respond to HTTP requests. In order to deploy this application to production, we’ll also configure a GitLab CI/CD pipeline so as to dockerize it and deploy its container to a Kubernetes cluster.
Serving a Keras model using Tensorflow serving and Docker
A Keras model can be created in various ways, for example using the <a href="https://keras.io/getting-started/sequential-model-guide/" rel="noopener noreferrer nofollow">sequential model</a>:
Gitlab CI commands for TF serving
This is an example .gitlab-ci.yml file which can be used to containerize and deploy a tensorflow model
Docker restart container when docker restarts
Simply add the following flag when using docker run
NodeJS app dockerization
NodeJS apps can be containerized using the <code>docker build</code> command. This article is based on <a href="https://nodejs.org/de/docs/guides/nodejs-docker-webapp/" rel="noopener noreferrer nofollow">this guide</a>.
Self hosted Docker registry
When using the <code>docker pull</code> command, container images are by default downloaded from docker hub, the official public registry for container images. However, for some projects, images are better stored on a private platform. This can be achieved by hosting one's own docker registry.
Docker behind a proxy
Docker does not use environment variables for proxy configuration. This article presents how to configure Docker to use a proxy.
Application containerization

Let's imagine a developer building an application on his computer and that this application is meant to be deployed on a different machine (production environment). In order to execute properly, this application requires multiple libraries, binaries and packages. For example, a Python program requires the Python interpreter as well as all the imported Python modules.